Before knowing what a spy phone is we must know what a spy camera is. In the simplest terms, a spy camera is a kind of hidden camera that records people, be it audio or video, without their consent of people. The term hidden camera has gained much praise and popularity after it was shown in the pop culture heavily, especially in shows based on investigative agencies.
Hidden cameras can be used for many purposes. Most of these purposes fall in three categories or motives such as:
- – Surveillance
- – Spying
- – Security
- – Documentation
Many people confuse the CCTV camera as a kind of spy camera. Closed-circuit television cameras ( popularly known as CCTV camera) are the most popular means of surveillance. While they are discreet, they are not entirely hidden which excludes them from the category of hidden cameras.
Spy camera usage holds its whole premise in being hidden and anonymous. As its name suggests it is used to spy on people by tracking their location and listening to conversations that the recorder is not privy to.
Software turning cell phones in spy cams
A spy phone, in simple words, is described as a phone device that is fitted with a listening or recording device. Earlier, a special device would be brought for this purpose but now more often than the recording and listening device is included in the phone only. This change is often done through a voice recorder or other software or app manipulations.
With the advancement in technology, there is an advent of software packages that can change normal software into a spy phone. This conversion happens in a few minutes. According to experts, even though this conversion software have become fairly common, it is still not easy to find a reputed software that does the needful.
The usual manner in which spy software is run is such that this software allows people to hack into a phone. Once the person successfully hacks into a phone then they will be able to read texts, check call logs, look at internet search history, and even listen to an active phone conversation. The problem with these programs is that they are very complex and require heavy coding to complete. A spy phone or a device that is used to record a conversation without consent are calling bugs.
The legal implications of using a spy phone
One has to be careful while using the spy camera as it comes in a range of many laws related to surveillance such as rules about phone tapping, recording conversations without consent, and sting operations. If someone is caught doing these actions without being within the limits of the law then they can be imprisoned and fall in grave legal trouble. The purpose of spyware is not limited to just recording and listening. It also allows one track where a cell phone is at a certain time. The precise satellite technology helps one do the tracking. The easiest way to create a spy cam is by installing a spy cam feature on your phone. There are many functions of a spy cam such as they can be used for tracing the kids and to monitor your staff. There are many working parents who use spycam to keep an eye on their kids.
Improvising the voice recording as a spy phone
One way through which the spy cam and its use were altered or outsourced completely was by voice recorders. People would put open the voice recorders and record conversations or they would leave their phones with voice recorders and hear what people are saying behind their backs. It is also used to protect one’s property from invasion. Spycams are also used by government and investigative agencies to undercover crime. There are both positives and negatives of having easily accessible spy cams.
The most prevalent and popular kind of spy cams is cell phones. These are often used due to their common use, the ease of manipulation, and easy availability. Another reason why mobile phones are more commonly used as spy cams is that the laws related to phone tapping do not apply to them. If you manipulate landline phones then you can also fall in legal implications that are subjected by the phone connection provider company. Besides, tampering or changing a mobile phone is easier than tampering other devices.
Spy phones and hidden camera
Today all phones have cameras that are not so discreet. People who are creative, resourceful, and improvising are making use of these cameras as spy cams. This improvisation has led to a decline in purchasing an actual spy cam. However, when the stakes are high then one should not depend on amateur or normal camera phones. The regular cell phones have limited features that might ditch the user at some point or may not produce the kind of results one is looking for. While spy phones can record a wider angle from their camera. They can catch low voices with clarity and have additional features that allow them to be opened via motion sensors remotely. Spy phones also have features that transfer their recordings to another device live this makes sure that even if the spycam gets damaged, the content it gained is protected. Spycams are also more discreet than mobile phones, they can be hidden easily without detection.
Tracking with a spy phone
A major part of spy cam also involves tracking a device. Cell phones have a monitoring system that is supported by GPS monitoring and spy cams make use of this same technology. It is suggested that if your main motive is to track someone’s location then you should simply install the tracking software in a second-hand phone, instead of specifically buying a spy cam. This option is cheaper and more convenient. Another reason why a phone is better suited for tracking is, even if it gets discovered one will not be too suspicious of a cell phone as they would be of a foreign-looking device.
Surveillance or spying via cell phones can involve bugging, monitoring, tracking, interception and recording of messages and conversations. Spy phones include the feature of tracking that can be done by GPS device or application embedded in a system or it can do by mobile phone signals. In the United States of America, government agencies and law enforcement branches have the authority to monitor the movements via mobile phone signals, but they can do this only after they getting orders from a court that permits them to exercise tracking.
Different types of spy cams
The thing about spy cams is that they should not look like spy cams. They should be discreet enough to be merged with regular household items in a way that no one suspects them to be cameras. Over the years technology has advanced so much that hidden cameras are now available in smallest and most versatile forms such as a pen.
One can use these cameras for their purchases and can also be careful if they are suspecting themselves to be taped or recorded. Here is a list of some different types of spy cams that have been successful around the world.
Hidden camera in the form of USB storage stick or a pen drive
USB storage sticks and pen drives are one of the most commonly used devices that are used in offices today. These hidden cams have been used to expose corruption in the corporate world and government offices alike. It is not uncommon for people to use these devices in daily office interactions and hence the spy cam is easy to integrate into a work-like environment.
The camera lens in these USB storage sticks is located at the posterior side which is opposite of the USB plug. This form and positioning of the spycam allow the camera to integrate seamlessly without any threat of detection. The spy camera can be a camera recorder, a voice recorder, or both.
Spycam as a shower gel or other bathroom essentials
The legality of using these spy cameras is very specific. In some places using spy cams in intimate spaces like washrooms, locker rooms, and dormitories are very stringent. Therefore it is advised that people who are making use of these devices have all necessary clearances and follow precautions while making use of this kind of spy cam.
As the name itself suggests, these are hidden cameras that are disguised as shower gels or shampoo bottles. They are made in a way where the top part of this product is made to hold shower gels or other products and the bottom part holds the camera and the recorder.
The top part of the bottle is refillable so that it can be used again and again. These cameras are made water-resistant because of the territory where they will be placed.
These cameras are notorious for capturing voyeuristic photos of unsuspecting people in rentals and public trial rooms. They are one of the most expensive types of spy cams. One thing that one needs to keep in mind as they use this product is to see if the bottle is passable as a legitimate shower gel. Often the packaging of these products bear the name of an old shower gel that has long surpassed being in the market. This small detail can give away the hidden camera so one should take care of this seemingly useless detail.
Spy Cams as AC adapter
These kinds of cameras are very popular in industrial settings even though they can be assimilated in almost most environments such as office spaces and even homes. These cameras are very easy to plug in the walls and genuinely look like they are a part of air conditioning ecosystem. To make them more believable, these cameras also come with their own wire that can be plugged in an electric socket for show. These cameras can do both recording and camera recording.
However, since they are attached near as they have limited zoom in option and they cannot catch faith conversations because of their positioning. These cameras have a wide-angle recording that makes them cover a large field as height affords them that coverage.
The advanced kind of live cams also come with a WiFi connection that allows a person to live to stream the recordings or save it somewhere else in case they do not get enough time to retrieve the AC adapter spy camera.
Spycams and tissue boxes
These kinds of spy cams are integrated into a tissue box or a toilet paper roll in an unsuspecting manner. The inclusion of spy cam does make the box bulkier but when it is planted in a real-life setting, one does not suspect anything. One can simply put them on a dressing table or a car dashboard and nothing will look out of place. The tissue boxes that have a spycam do not usually have branding, they are used as artisanal tissue boxes. With the advancement in technology, sleeker cameras are coming in the market that is reducing the bulkiness of these tissue box spy cams. These hidden cameras are moderately priced and are sturdier than other hidden cameras as tissue boxes sometimes fall and are often displaced.
Spy Cams as electrical outlets
Spycams are also hidden in many electrical outlets that can be used daily by unsuspecting people. These cameras and recorders are very tiny and can be hidden in congested spaces like electric socket holes. The rechargeable ones have adhesive backs that are very sticky and can be placed in a variety of surfaces, if not electric charging points. These cameras are very hard to place as well as really tough to retrieve.
Prevention and protection against spy phones
Long before the era of cell phone domination, only one way of cell phone surveillance was popular. This method was called wiretapping. Wiretapping was had now been replaced with more modern methods of spying and detection. Wiretapping is also called electronic eavesdropping. Today software does the complicated work of wiretapping.
Organizations such as CBI, FBI, Interpol, etc have always used phone surveillance to investigate and search criminal activities. Previously, practices like wiretapping were performed by only a few people and agencies that had infrastructural support to execute these actions. Normal public did not have to worry about their breach of privacy and the dangers that came with it. However, with the ease of use, accessibility, and affordability, spy phones are not just being used by federal and investigating authorities. They are also employed by people who are into blackmailing and use sensitive information as ransom.
Its misuse has also caused people to be more cautious about how they navigate public spaces or have conversations with their near and dear ones. Hostile governments and dictatorships make use of spy phones to keep a track of opposition and protesters in a way that seriously undermines their life and freedom.
Spy phones have resulted in the massive breach of privacy and this why people are becoming very cautious of how to prevent their phones from the invasion of other spyware software.
Here are a few safety measures and tips to know if their phones are being tapped and how one can protect their phones:
- One should prevent strangers from using your cell phone as they can install a bug or spyware.
- One must not give or share their passwords to strangers and do not activate the feature of saving passwords on web pages or portals.
- If you are extremely concerned about the hacking of your phone using a spy phone then pull the battery of your phone out when it is not in use.
- You can also employ processes like phone jamming and faraway cage.
- Make sure your microphone remains disconnected when it is not in use.
- One way of detecting if your phone is under surveillance or not is by keeping a close eye on it. If your phone starts pinging without any cause and you hear beeping sounds when you are engaged in a conversation then you should get your phone checked.
- The phones that are controlled by outside or cell phones that are in reality spy phones feel warn even as they are not being used physically. These phones get heated up because their operations are controlled remotely so even though the cell phone appears to be at rest, we know the spy phone is being run and hence they get warmed up despite the lack of physical activity.
- Regularly delete your browser history and do not activate any web cookies.
- Change your passwords (phone password, an e-mail account password, etc) regularly.
- Before starting any important meeting, make sure that no idle phones are lying around and ask the attendees to switch off their phones.
- Install good anti-malware software in your phone so that it alerts you if spyware tries to break in your phone’s operating system.
- Install a password manager to make sure your online transactions and other practices are safe.
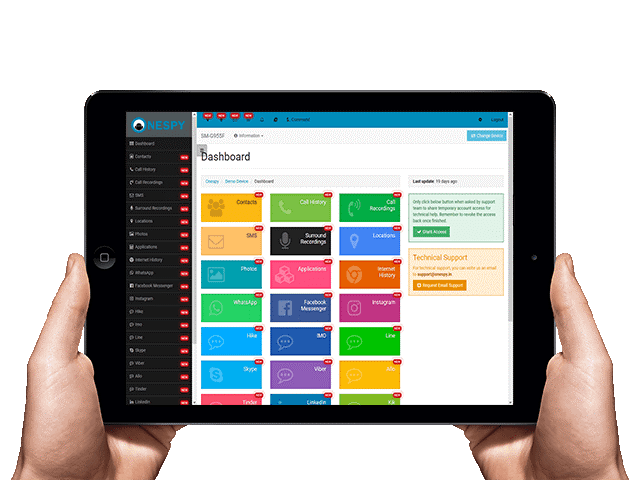
Smartphone Monitoring Features & Benefits
Smartphone monitoring has many features and benefits that go beyond the simplistic desire of hearing conversations behind one’s back. The fact that enabling features and benefits out of smartphone monitoring is very easy goes on to show why it has been adopted by so many people around the world.
- Some of the features of a cell phone spying software are:
- It allows observation of the subject’s phone location live and can display it on a digital map.
- It can activate microphones that can record and forward conversations.
- It alerts the spying or tracking agencies when the tracked phone is brought in use.
- Gives access to mobile texts and call logs.
- It helps one gain access to notes that are kept in a phone.
- It blocks unwanted websites and apps. Parents often use this feature to block problematic websites. It is widely used during exams when parents block applications such as Pokemon Go which is used heavily by kids.
How to use a new spy phone
Unlike landline phones that needed difficult surveillance procedures, cell phones are very easy to track and monitor. There are always vulnerabilities in cell phone systems that can be tapped and via these vulnerabilities, the security can breach. The hacking and surveillance infiltration systems have advanced enough to locate backdoor entries even in most secure operating systems. A good hacker will have codes and ways to bypass detection and elimination by best anti-malware software. It is because of this advancement in white hat hacking area that the smartphone monitoring systems are gaining popularity and users.
Some spy phones are really easy to use while others are more complex. Before understanding what is the best way to use spy phones it is important to distinguish between two types of spy phones. The first type consists of special cell phones that are made for the sole purpose of spying and surveillance. These devices look like a mobile handset but they do not have features of full-fledged mobile phones. Their main purpose is of capturing wide-angle views with clarity and record high-quality audio. These devices can be controlled remotely and are used by large investigative authorities only.
The second type of spyware is the one that is being controlled by software systems. Any normal mobile phone can be converted into a spy phone through this method. This method is more prominent and in use today than it was ever before.
There are three ways in which you can use a software-enabled spy phone:
1. First of all, go to a safe software downloading platform such as Google Play and download a well-rated smartphone monitoring software.
2. After downloading the software, wait for it to get installed. Once it gets installed, you will be asked to give your credentials to activate the app. In some cases, you will be asked to give a license key or one time password to active the software on the phone number that is the target.
3. The last and third step is to finally monitor the surveillance.
Once the software is activated you will be free to monitor the target number according to your wish. Usually, you will be able to track the location, access web history, intercept texts, access call logs, notes, and in rare and advanced cases hear ongoing cell phone conversations too.
You can monitor the target cell phone from your computer, laptop, tablet or other internet-enabled devices. It is easy to use these monitoring devices; one just has to read the instructions carefully before jumping on the usage of it.
It is very imperative to notice right now that the person using this monitoring does so within the confines of laws.
Even though there are different instructions for different operating systems and apps the above-mentioned steps are common to all programs.
Features of a Good Smartphone Monitoring software
There has been an influx in the number of smartphone monitoring system around the world. It is very important that while selecting one such system or software, the buyer keeps a few things in mind before committing.
Some basic features that should be in all smartphone monitoring software are:
- The software should be user-friendly. Its interface and design should be in such a way that experts, as well as beginners, learn to use the software appropriately without any problem. If the software is hard to grasp and can’t be used by people or requires heavy coding and complicated instructions then its not a good software or program.
- The smartphone monitoring system should be very fast. It should not take forever to set up in your cell phone. In today’s fast-paced world people do not have time to wait for hours just to get the software downloaded. A good monitoring system will get installed within minutes without disturbing the overall system of the cell phone. The installation process will not require any heavy overhauling or heavy coding. It should be completed within around 10 to 15 minutes.
- The monitoring system should be lightweight so that it gets installed even in devices that are low on storage or memory. The software should also be able to work within slow internet. If the software takes too much storage and its functions are only workable in fast internet then the software will cater to only a small segment of the population.
- The software should have the latest technology and features installed in it. There is no point in having a monitoring system that is not up to date.
- The software should apply to different kinds of operating systems such as Android and iOS. If the software is not compatible with several phone systems then it will not make a good phone.
- Whichever company you choose for using a smartphone monitoring software, make sure that the ones you pick are verified and can be downloaded through safe and legal channels such as Google Play.
- Smartphone monitoring software runs the risk of being Trojans that can end up disabling the devices and hacking into the system. Hence, one should always do a background check of the app before downloading it.
- Other than this, your monitoring app should have a reliable customer care support service with helpline or live chat feature.
- For all paid subscription models, it is of utmost importance that the software company gives you a free trial period to test their services. This trail period lets you know if whether or not your needs are in alignment with what the company is offering. The trial period usually runs between 10 days to a fortnight. · Another good way of knowing about the monitoring software is by looking for verified user reviews and feedbacks. If the user reviews are good then you should give that software a heads-up.
Smartphone Monitoring Features & Benefits
It enabled people to do several things that facilitated surveillance, such as:
- Accessing internet search accounts such as bookmarks, search history, emails, and web calendar.
- Access to social media sites such as Facebook, Skype, LINE, tinder, WeChat, WhatsApp, and Google Hangouts.
- It also allows remote controlling of an internet-enabled device. This controlling means restricting calls and messages. It can also result in blocking certain websites and apps. These features are mostly used by parents who are trying to maintain a semblance of control in their kids.
- The advanced versions of this app also allow logging in the email accounts and installed applications.
- This app can be used to activate geofencing and GPS tracking.
- One must be very careful while using this app as it is prone to hacking. Hacking can lead to disclose of sensitive information at the wrong hands and can lead to misuse.
- Accessing internet search accounts such as bookmarks, search history, emails, and web calendar.
- Access to social media sites such as Facebook, Skype, LINE, tinder, WeChat, WhatsApp, and Google Hangouts.
- It also allows remote controlling of an internet enabled device. This controlling means restricting calls and messages. It can also result in blocking certain websites and apps. These features are mostly used by parents who are trying to maintain a semblance of control in their kids.
- The advanced versions of this app also allow logging in the email accounts and installed applications.
- This app can be used to activate geofencing and GPS tracking.
Best Smartphone Monitoring softwares
Here is a list of some of the best monitoring software in the world:
mSpy
Very popular software that deals with a spycam is called mSpy. It is officially promoted as parental control monitoring software. It works for operating systems such as Apple’s iOS, Android, Microsoft Windows, and macOS. This software’s functions can be easily explained as monitoring and recording.
o One spy
One spy is one of the most downloaded phone monitoring software. It is sold as a parent and employee monitoring device. It has all the legal verifications that are needed. One can monitor almost all features of a cell phone once you get this software installed. It is very user friendly and has an easy to use control panel
It takes around 15 minutes to make use of spying features for the first time. Internet data is important to establish on the targeted device, without which the information will not be shared with you. If there is no internet or slow internet then the timings can be different. The updates and information become live after the first review.
One spy also offers refund policy within 10 to 15 days of the applicable purchase. One spy comes in three different versions that are based on one’s needs and budgets. These versions are Prime, Budget, and Elite. They can be purchased on a monthly, quarterly, or annual basis.
The customer support provided by Onespy is also very helpful. The bank level encryption technologies employed by Onespy make it very safe against hacking. It also has additional features such as hidden call recorder, live location tracking, live WhatApp tracker, hidden voice recorder, etc.
XNSPY
XNSPY IS said to be one of the safest apps that monitors tablets and mobile phones. It is also considered to be very easy to use because of its simple design and interface. It is used around the world as a nanny cam and child and employee monitoring tool. This software allows people to keep an eye on phone activities and in turn the actions of their children and employees. It enables people to remotely keep an eye on all call records, web history, and text messages.
It also grants access to the media files of the number that is under surveillance. This way one can know what photos, songs, and other media files are being shared, produced, or seen by their child or employee. It also has a very accurate and fast GPS tracking system that lets you know the location of a person via their phones.

XNSPY also has an intricate system of alerts that notifies the surveying party if a certain word being used in the mobile phone or a tablet. Alerts can also be set for a geographical location that will activate alerts if a person surpasses a certain location. This kind of alert is called geofencing and is used by parents to see if their child is at home or not.
XNSPY also has a quick system of statistics that summarises the findings of the surveillance. Here the app gives quick numbers for revelations like 10 most frequently visited websites, 5 most called numbers, and 5 most received numbers. It also gives people quick numbers about the top 5 call durations. The additional feature of Call Time Activity Punch Card also documents the alls made at designated hours of the clock.
This software has also assimilated the advanced feature of monitor keystrokes that work with instant messaging apps such as Facebook, Viber, and Whatsapp.
Monitor keystrokes from instant messaging apps, including WhatsApp, Facebook, Facebook Messenger, Skype, and Viber. Perhaps the most powerful thing about this app is its ability to make one again access to all calls and texts that are being made by someone else. This is the whole purpose of making apps like these.
One can very easily, remotely tack their loved ones by reading the texts and media they are sharing, which includes knowing about the appointments they have fixed. This app also wifi logs. If a person makes use of this device without the consent of the person that they are targeting then this supervision can result in a breach of privacy litigations and other legal implications. This software has both paid and unpaid versions. It offers great value of money.
Mobile Spy
Mobile Spy has its name in the list of some of the best mobile monitoring software. Upon its subscription, one is sure to get world class software products and support. This software has very quick and easy downloading. One can also request easy downloads on Mobile Spy.
Mobile Spy offers a very concise list of step by step instructions that guide the user along with all steps of the way. It also has a really helpful and approachable tech support service that gives rapid online support to all its subscribers. All subscribers of Mobile Spy are eligible for free upgradations. This software is moderately priced and is compatible with most operating devices. These two things further enhance its accessibility.
Experts explain Mobile Spy as hybrid software that permits the user to supervise a cell phone in real time. It easily logs into both Android and iOS service effortlessly via a smartphone or a tab.
One should inform their employee or child that their phone devices will be monitored. The app has an option of alerting the subject that their phone is being monitored. This feature is optional though; one can also track and supervise a subject without informing them.
How Mobile Spy works is that, once it is set up completely, the app in log in several phone activities and forward you all the information via internet connection. One just has to log in to view the results. You can log in from any device or browser. On its live control panel, one can find out the live location of the targeted phone and also watch its screen. There is an option of availing a 7 days free trial of this app. One can also read all texts of the subjected phone, its call logs, social networking sites, web history, and all media. It also allows people to block undesirable websites by just a few commands. All these factors make Mobile Spy an all-rounder application.
There is one feature that makes Mobile Spy different than others. It is Profanity alert. Basically, this feature sends alert when a profanity is written or viewed. This feature is usually used by adults who want to supervise their kids.
Another stand out feature is Geo-Fencing. It lets one set boundary after which they don’t want the device holder to travel. One your cross that geo-fence, the person who has put the geo-fence will be sent alert messages. Then there is another alert system of contact alerts. Here you are informed of every call or text the numbers that you have placed under these alerts.
Then there is an alert of the intrusion ping. Here whenever someone puts the wrong pin or command one’s phone an alert is released. This is done to prevent manual intrusion in a concerned phone.
In the end, there is a feature of custom alerts. In custom alerts, the alerts are released when someone enters, uses, or receives keywords that are marked by the supervisor.






Leave a comment